Tokens; ICOs; Security tokens, and their types!
13 min readApr 22nd, 2020
Traditionally, securities represent an ownership position in a publicly-traded corporation, rights to ownership, or a creditor relationship with any governmental corporation/body. Security Tokens are digitized versions of the same. A security token is a tokenized, digital form of these traditional securities. To truly understand the technicalities behind the different types of Security Tokens, and what really makes them different, we need to talk a bit about Tokens and security regulations around them. If you’re already aware of this, you can skip this and head straight to the types of Security Tokens.
What are Tokens?
Pinpointing the exact definition of a token is a very complex task. Still, to give you a non-generalized definition - a token is basically a representation of an entity in a particular ecosystem. It could be stake, value, voting rights, anything at all. A token is not exclusive, as in, it is not limited to one particular role and can be used to fulfill various roles in its native ecosystem. Tokens are legacy items and are different from cryptocurrency coins. Bitcoin, Ethereum, and other cryptocurrency coins are independent of a platform and can be used as a currency even outside their environment. Tokens, on the other hand, can be used within their environment, in their platform. A token, represents an asset or utility that a company has and they usually give it away to their investors during a public sale called ICO (Initial Coin Offering).’What is an ICO?
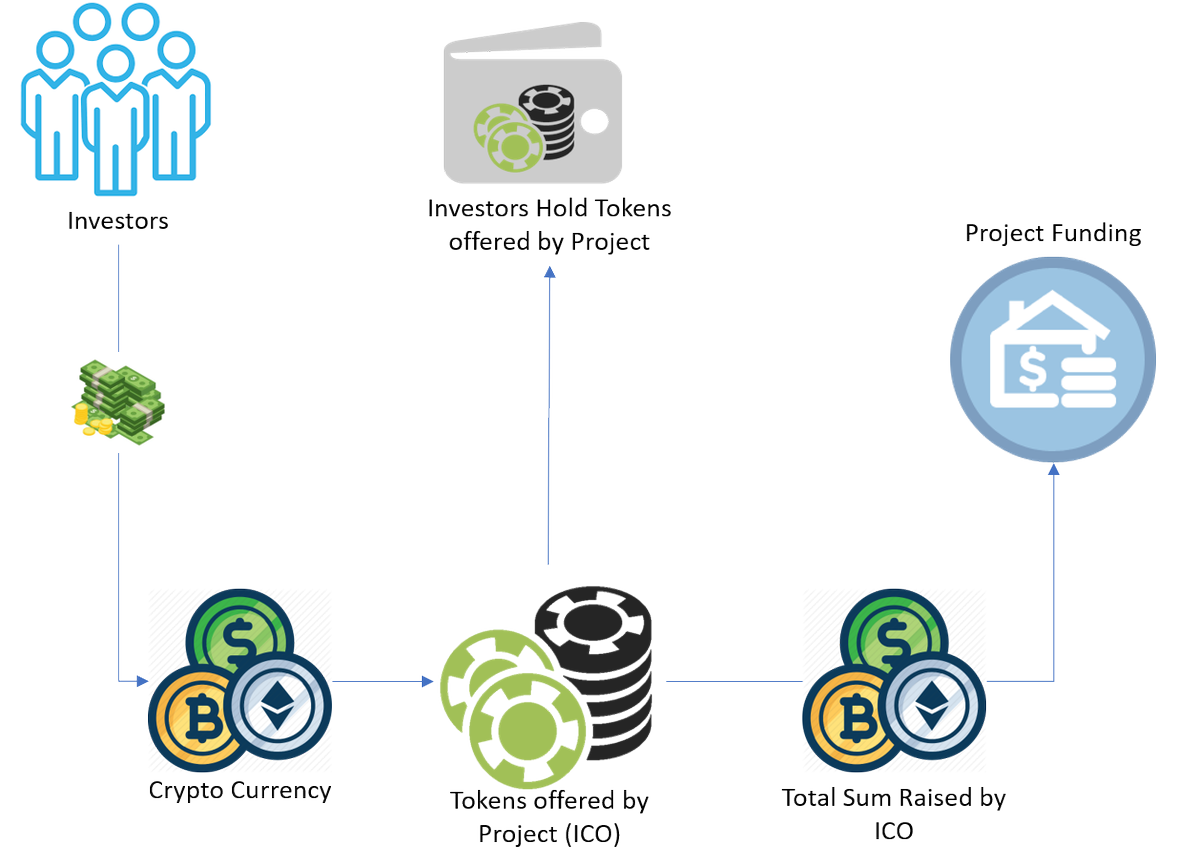
Short for Initial Coin Offerings, ICOs are essentially sales that are crowdfunded - consider it the cryptocurrency version of crowdfunding. Through the years, ICOs have proven their mettle and managed to accomplish amazing tasks including: - Providing an easy path for DAPP developers to get the required funding for their projects. - Simplifying the process of investing in a project, as anyone can become invested in a project they are interested in by purchasing the tokens of that particular DAPP and become a part of the project themselves.Okay, how does ICO work?
To begin with, the developer issues a limited amount of tokens. In doing so, it is ensured that tokens have value and the ICO has an overall goal to keep up to. These tokens can either have a pre-determined, fixed price, or the price may fluctuate depending on the way the crowd sale is progressing. The transaction takes place in a pretty simple way. Anyone who wishes to buy the tokens can send that particular amount of ether to the designated address. Once the acknowledgement of payment is made, they will receive the respective amount of tokens. Everything is decentralized, so the success of an ICO depends on whether or not it is properly well-distributed and if a majority of its chunk is not owned by one entity.In the last EOS ICO, the total amount raised was a whopping 4 billion dollars in a year, which is till date the biggest ICO ever. Further, TechCrunch points out that ICOs have been delivering at least 3.5x more capital to Blockchain startups than Venture Capitals since 2017
How Does a Token Gain Value?
It’s important to know the functions a token can perform to gain more value. Broadly, there are three tenets to token value: - Role, - Feature, - Purpose. Let’s examine each of the roles that a token can take up:Right
The holder possessing particular tokens gets certain amounts of rights and access within the entire ecosystem. For instance, if you have DAO coins in your possessions, you have the voting rights inside DAO to decide the future of projects in terms of funding.Value Exchange
Tokens create an economic system internally, within the project itself. They can help sellers and buyers make trades within the ecosystem. In doing so, tokens help people gain rewards on completion of particular tasks. This task - of creating and maintaining internal economies and incite value exchange - is one of the tasks of tokens.Toll
Often, tokens can also act as a toll gateway for you to access certain functionalities of a particular system. For instance, you require GNT (Golem Tokens) in GMT to access and leverage the Golem supercomputer.Function
These tokens help enhance the user experience of the holders, too. Brave (a web browser), offers BAT (Brave Token) holders the rights to add advertisements or other attention based services on the Brave platform using their tokens.Currency
As mentioned earlier, they use Stablecoins, and hence they can be used to store value, which can then be used to conduct required transactions - both internally and externally.Earnings
Helps in the equitable distribution of profits or other related financial benefits among investors in a particular project. So, how does all of this help with token valuation? A token, in order to become more valuable, must fulfill one or more of the above-mentioned properties. The higher the number of properties it covers, the higher is its evaluation. So far we’ve covered what a token is, how is it distributed, and the ways for it to gain value. Now, let’s move to Security Tokens and some tests that have been established over the years to determine whether or not a token is a Security Token.The Howey Test: What is a security token?
In 1946, the Supreme Court was presented with a unique case. It was SEC vs Howey, and it would go down to lay the foundation of what is now infamously called the Howey Test. The case was about establishing a set of rules on whether or not a particular arrangement involves an investment contract. Without getting too much into the legal aspects of things, The conclusion of the case was that any transaction will be called an investment contract if it fulfills the following criteria: - It requires investment of money. - The said investment is in a common enterprise. - There is an expectation of profit from the work of the promoters or the third party. The term “common enterprise” is, honestly, open to interpretation. Many federal courts, however, define it as a horizontal enterprise where investors contribute their assets and money in order to invest in any project. Though the initial Howey Tests used the term “money”, the term was later expanded to include investments and assets other than just money. However, there is another thing to consider when determining whether or not an asset has a security - the control of profits. Whether the profits that come out of investment are in the hands of investor or is it completely out of hands? If it isn’t in investor’s control, then the asset usually has a declared security. Bringing ICO and tokens back in context; if any token meets the above-mentioned critera, then it can be regarded as a security. All these three elements have to be met for a coin to classify as security.Other Alternative Tests
Howey Test wasn’t the only test that was used to find out whether or not an asset is a security or not. Not so far back from today, in 1990, the court developed a family resemblance test and provided a way for contract creators to show that their contract have a “family resemblance” to other investments and hence cannot be called securities. Some states tend to have their own rules and regulations and registration requirements around securities - these are called as “Blue Sky” laws. According to Wikipedia, “The first blue sky law was enacted in Kansas in 1911 at the urging of its banking commissioner, Joseph Norman Dolley, and served as a model for similar statutes in other states. Between 1911 and 1933, 47 states adopted blue-sky statutes (Nevada was the lone holdout). Today, the blue sky laws of 40 of the 50 states are patterned after the Uniform Securities Act of 1956. Historically, the federal securities laws and the state blue sky laws complemented and often duplicated one another.”The DAO and SEC
The above-mentioned Howey Test and securities have been a source of heated debates - especially after DAO tokens failed to pass the test and were deemed securities. It wasn’t too long ago when a group of developers started DAO. They said, “All these decentralized projects, but no way to get funding? Probably because it takes money to make money. We’re going to write a code, and, in exchange, people who buy the tokens will be given whatever profits are made from those projects. We’ll rack our brains on the code, they’ll pick the projects. The projects will flourish - win win for everyone! The SEC firmly said, “That’s a security.” The DAO developers replied, “No, that’s just selling tokens.” Eventually, the SEC ruled: “That’s a security” – because there was an investment of money. And a common enterprise. With the expectation of profit, primarily from the efforts of others (therefore, it passes the Howey Test). But why was this intensive investigation and ruling done in the first place? The answer is quite extensive, so, here’s the tl;dr version: - There was a flaw in the DAO smart contract. - The hacker exploited that flaw and performed re-entrancy attack. - More than $150 Mn. worth of Ether was siphoned away. A lot of people intervened, investigated, and tried to get this matter in control, but nothing worked. That’s when the SEC intervened to protect the interest of investors - and deemed these tokens as securities. Now, that should clear all the air around what is a token, what are securities, and what is a security toke. Summarizing the above discussion real quick: Security tokens, functionally, are similar to traditional security - except that Security Tokens are Blockchain based and support partial ownership. Security Tokens are programmable units of security that fall under the same laws as regular seurity. Security tokens eliminate the need for immediaries by using smart contracts. So, any loan tokenized on Blockchain can easily make payments without using legacy middlemen - like banks and other financial institutions. Originally, ICOs were thought to be the way ahead, but due to scams, regulations were made stricter around it. STO, simply put, is the legalized version of ICO. An article from Securities.io mentions that one of the key reasons for the collapse of ICOs have crashed is their flawed business concepts. The number of credible projects is disappointingly low as compared to scams and projects that claim to “revolutionize” the world. As a result, these companies struggle with compliance issues and efficient funds utilization. All of this led to the rise of STOs. Projects have to go through proper legal channels with governing entities before raising funds. Ideally, should the company end up closing, it would ultimately be a failed investment. And if said company were a scam, they can be traced back by authorities. Now, let’s look at the various types of Security Tokens. Types of Security Tokens. Broadly, there are three types of Security Tokens: - Equity Tokens: These represent the value of shares issued by a company on the Blockchain. Equity tokens differ from traditional stocks in their methods of recording ownership. In case of traditional stocks, the purchase is logged into a database and the records are then represented by a certificate. Equity tokens, however, maintain records in an immutable Blockchain. This essentially digitizes the entire process of recording ownership and gives a more transparent system to work with. Owning equity tokens entitles the holder with a portion of company profits and the right to vote. It should be noted that these tokens are not limited to just the initial funding stages, although most companies can be found offering these only during the seed round. The equity token ecosystem offers the following benefits: - Allows investors to invest in compliance-friendly Blockchain companies. - Provides new fundraising and bootstrapping models to young startups. - Defines a framework for regulators to assess the funds raised during the project. ICOs, too, provided on opportunity for young startups to seek funding, but they came under major scrutiny due to lack of ownership clarity. STO resolves this by keeping the entire process compliant with the laws. Documo is one example of an equity security token. - Debt Token: Debt-based security tokens are representative of assets like real estate mortgages and corporate bonds. Their prices are directly dictated by two strict factors:- Risk
- Dividend.